AT+AKSEEDNO Calculator
The AT+AKSEEDNO calculator makes it easy to answer the Samsung device challenge questions with the right AT command. This can calculate the proper response to give back to Samsung basebands for the AT+AKSEEDNO command. When sending AT commands, some commands may require AKSEEDNO challenge request and response before continuing, like with AT+IMEISIGN or AT+BLOBSIGN. If you want a new tool for running AT commands from your PC you should check out Phonlab AT command tool.
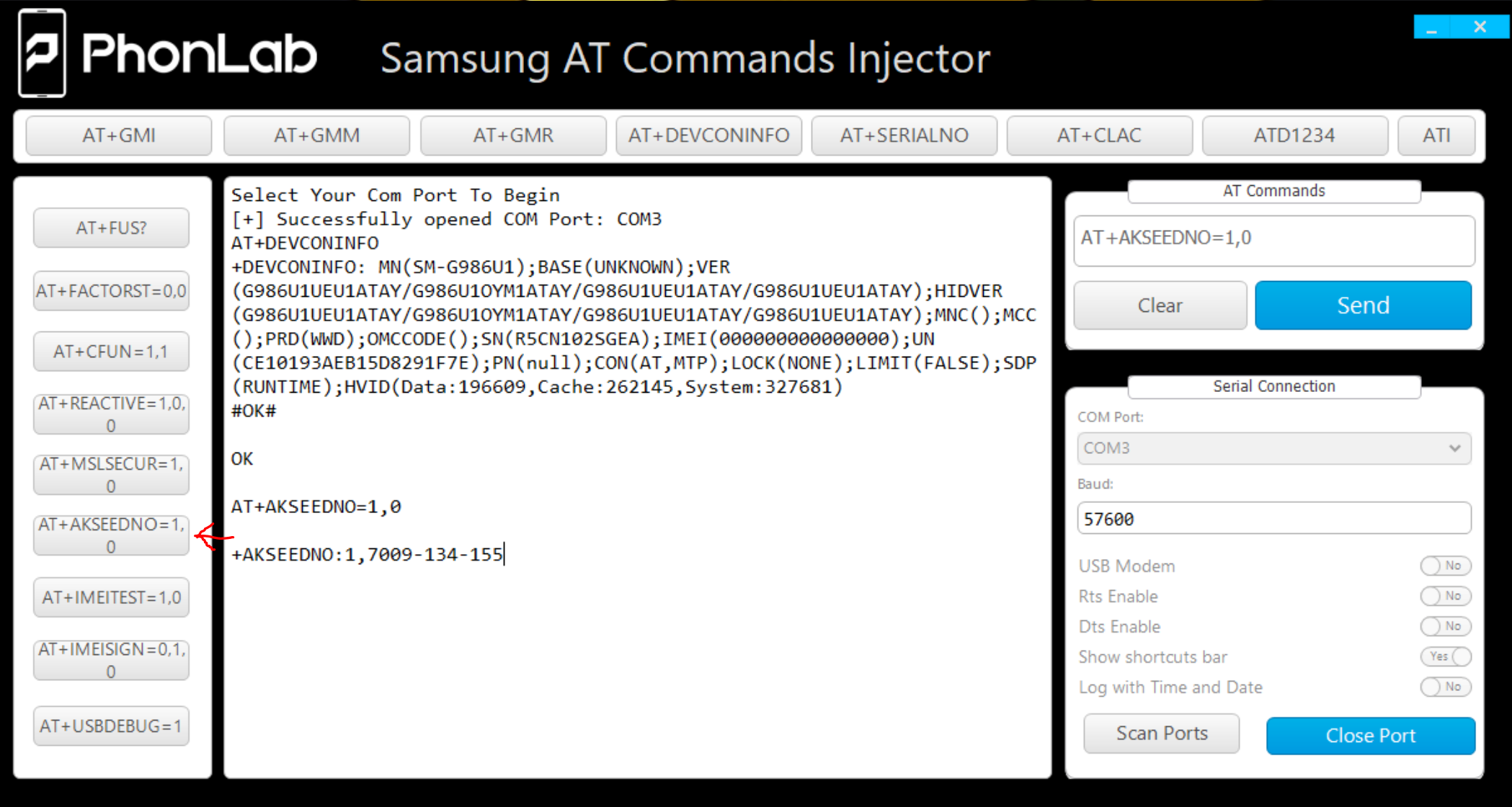
AT+AKSEEDNO=1,0
+AKSEEDNO:1,7009-134-155
akseed_calc.py 7009 134 155 you would run this command to get the output of 103-90-126
AT+AKSEEDNO=0,103-90-126
The nice thing about this challenge questions is that it is 100% mathematical which makes it easy to have a program that can calculate the answer link you can find here on Github. Using this program will require you to have Python with six module (2.7 or 3.x) installed on your PC. Once everything is setup you can run akseed_calc.py (number1) (number2) (number3) to get your numbers calculated for you.
On new Samsung device you can no longer run the AT+AKSEEDNO command because security has changed and this command along with many others has been block over the modem connection and will only return an error message. Not to worry because someone has come up with a nice little file that you can use from Android debugging bridge to send at command to the modem directly.
[+] Initializing: success.
[+] Model: SM-N970U1
[+] Processor: qcom
[] Main Menu []
[1] Send AT Command
[2] Reboot Upload Mode
[3] Wipe MSL New
[0] Exit
Enter Selection: 3
Wiping MSL….
Step 1…
Step 2…
Step 3…
All Done…
This is a small file that gets pushed to /data/local/tmp and then run in adb shell with command data/local/tmp ./AT once running on the device you can send AT commands to the device from the PC CMD window or powershell.
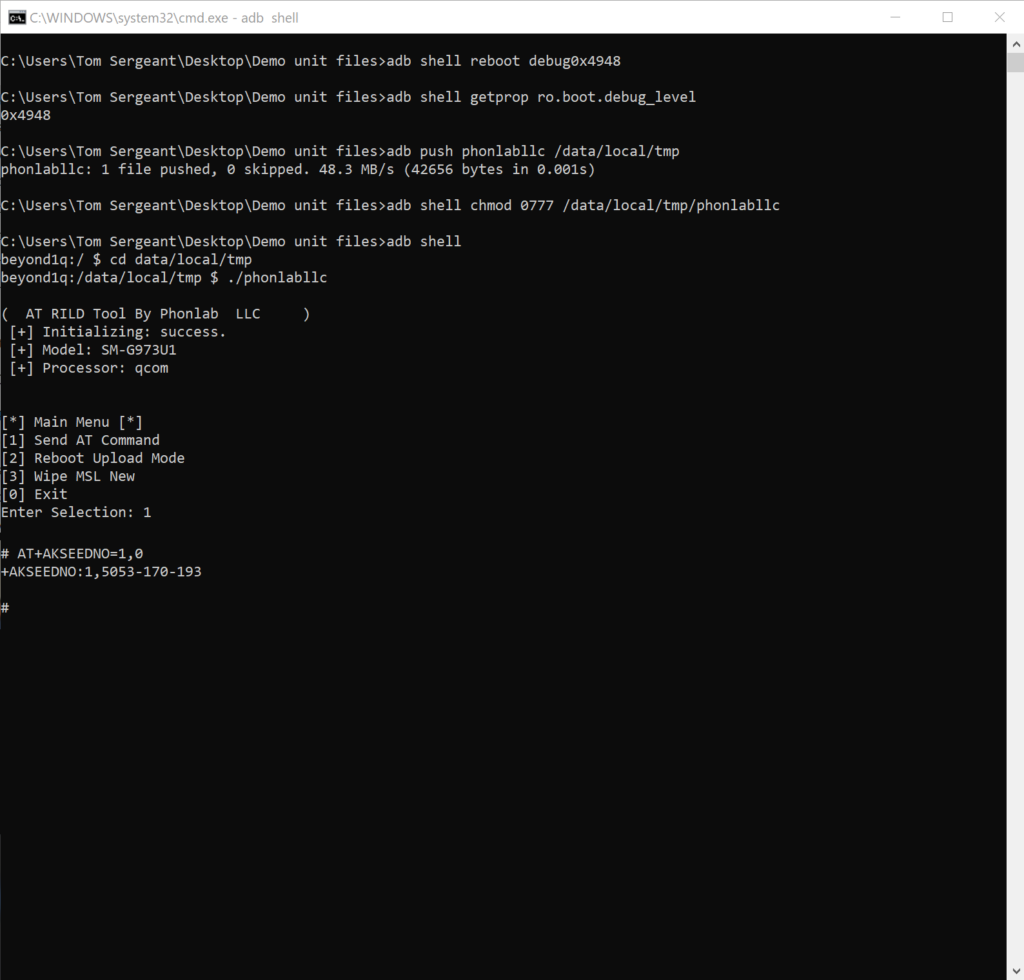
adb shell reboot debug0x4948
adb shell getprop ro.boot.debug_level
adb push AT /data/local/tmp
adb shell chmod 0777 /data/local/tmp/AT
adb shell to data/local/tmp to run ./AT”
Now you can run AT commands that where locked out before. 🙂

One Response
Hi, I am currently studying the Samsung RIL, if it is possible to share, how does the executable allow AT commands? Does it make use of Android RIL libraries? Or is it exploit based? Thanks you!
Comments are closed.